<--- Back to Details
| First Page | Document Content | |
|---|---|---|
 Date: 2007-02-27 09:35:26Block cipher Symmetric-key algorithm Playfair cipher Ciphertext Cipher One-time pad Keystream Cryptanalysis Cryptographic hash function Cryptography Stream ciphers Substitution cipher |
Add to Reading List |
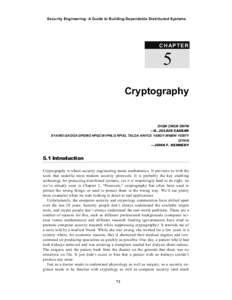
 | Influence of first two keystream bytes 2−7 Bias 1 Bias 3 Bias 5DocID: 1xV86 - View Document |
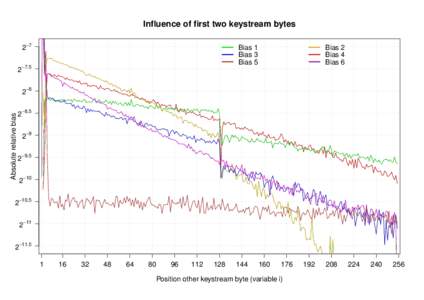
 | Keystream distribution at byteDocID: 1xTZC - View Document |
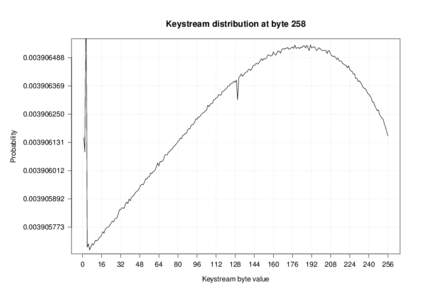
 | Probability of keystream valueDocID: 1xTVG - View Document |
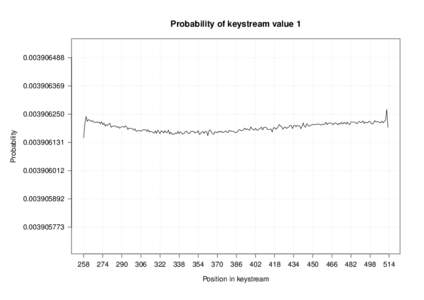
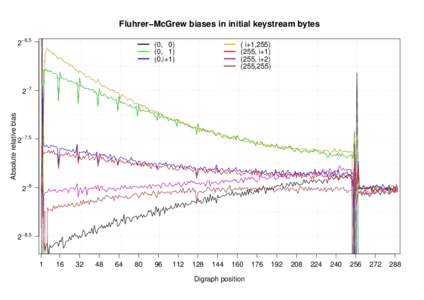 | Fluhrer−McGrew biases in initial keystream bytes 2−6.5 (0, 0) (0, 1) (0,i+1)DocID: 1xTHJ - View Document |
 | Biases in the RC4 keystream (128 bit uniform keys) Nadhem AlFardan and Dan Bernstein and Kenny Paterson and Bertram Poettering and Jacob Schuldt Royal Holloway, University of London University of Illinois at ChicagoDocID: 1tSaM - View Document |
 Security Engineering: A Guide to Building Dependable Distributed Systems C H A P TE R 5 Cryptography
Security Engineering: A Guide to Building Dependable Distributed Systems C H A P TE R 5 Cryptography