<--- Back to Details
| First Page | Document Content | |
|---|---|---|
 Date: 2014-02-25 14:14:07Outline of cryptography Side channel attack Edward Felten Cryptanalysis International Cryptology Conference Cryptographic engineering Elliptic curve cryptography Cryptography Lattice-based cryptography Pwnie Awards |
Add to Reading List |
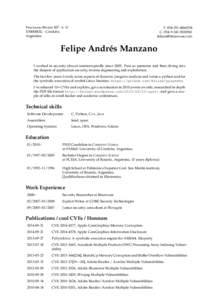 | Fructuoso Rivera ’A’ ´ X5000BOG - Cordoba Argentina TDocID: 1alNb - View Document |
 | Over 30% of Official Images in Docker Hub Contain High Priority Security Vulnerabilities Jayanth Gummaraju, Tarun Desikan, and Yoshio Turner BanyanOps {www.banyanops.com, } Docker Hub is a central reposDocID: 19EGD - View Document |
 | PDF DocumentDocID: 17aOm - View Document |
 | SAINTwriter Assessment Report Report Generated: March 20, Introduction On March 20, 2013, at 10:38 AM, a heavy vulnerability assessment was conducted using the SAINTvulnerability scanner. The scan discovDocID: 14nN4 - View Document |
 | Hayward Street Ann Arbor, mi usa (mobile ) + J. Alex HaldermanDocID: 12PEf - View Document |
 Nadia Heninger +[removed]Computer & Information Science Department University of Pennsylvania 3330 Walnut St. Philadelphia, PA[removed]
Nadia Heninger +[removed]Computer & Information Science Department University of Pennsylvania 3330 Walnut St. Philadelphia, PA[removed]